37,000 Plex Media servers exposed to the internet are being abused in DDOS attacks according to a new security report.
Plex Media Server is a personal media library and streaming platform available on Windows, Mac and Linux platforms. One of the attractions of Plex is the ability to stream your local media library to remote locations by exposing the Plex software onto the internet. This would, for example, enable movies to be watched while at work from your home media library.
When started, the Plex software probes the local network to identify possible streaming clients and compatible media devices. If it can locate the network router using SSDP (Simple Service Discover Protocol) it will also attempt to configure its UPnP gateway to route certain incoming traffic to the Plex server. Plex posted a notice in February that this configuration is open to abuse in DDOS attacks. The Plex software itself and its local network are not at risk, however it can be leveraged in order to attack a third party through a reflection DDOS attack.
What is a DDOS Attack?
DDOS – Distributed Denial of Service attack – is a malicious attack designed to take the target system or website offline, usually by sending a huge volume of traffic that overwhelms the server. To generate the large volume of traffic needed to swamp the target, many different devices are co-opted into generating the attack – hence the ‘distributed’ moniker. The devices used to generate the attack are usually botnets or networks of devices infected with malware and the owner is unaware of their part in the attack.
DDOS attacks can be used as part of a ransom strategy where the attacker demands payment to stop the ongoing attack.
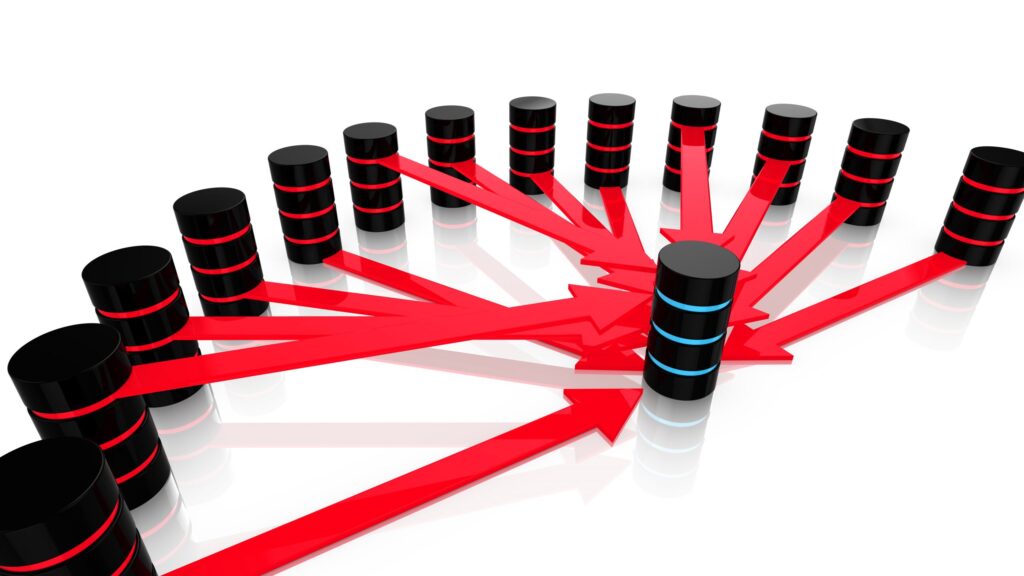
One of the techniques used to generate the large volume of network traffic needed in the attack is called reflection/amplification. This approach abuses legitimate network protocols that send larger responses to small requests. Thus, the attacker can transmit a small amount of data and receive a larger amount of network traffic in response – the amount of network traffic has been amplified. By spoofing the source IP in their request, the attacker can cause the response data to be sent to a different system – the target of the attack – hence the reflection. For example, the attacker device sends a 256-byte request to a system that’s part of the DDOS network (the reflector) and spoofs the source IP address, so it appears to come from a third device – the innocent target of the attack. The reflector innocently and correctly responds to the request and sends its larger response (4 kilobytes) to the target. Since there are, say, 1000 devices in the DDOS botnet, the target is swamped with 4,000k of consistent network traffic. The incoming DDOS traffic is from 1000 different IP addresses and so is hard to track or block by the firewall or network load balancers. It is not uncommon for DDOS attacks to deliver Gigabytes of data each second against their target.
How is Plex used in DDOS Attacks?
The exposed ports that Plex opens on the NAT router make it vulnerable to be abused as a reflector in DDOS reflector/amplification attacks. The exposed SSDP port can be probed using a UDP request that generates a response about 450% larger. With UDP the source IP address is easily spoof-able meaning the SSDP response can be reflected to another target.
Mitigation
Plex has posted a security updated and a new software version which now only responds to UDP requests from the local LAN, and ignores traffic from the public internet (WAN).
SSDP is designed for use in residential or small office networks and should normally not be exposed to the Internet.
Reviewing your firewall rules and other enabled protocols to disable all those not required will reduce the attack surface of your network. Regular security scans and external network penetration tests will ensure you identify any open ports which can be abused by attackers.


















“We were very impressed with the service, I will say, the vulnerability found was one our previous organisation had not picked up, which does make you wonder if anything else was missed.”
Aim Ltd Chief Technology Officer (CTO)