An unauthorised change to a script used by Codecov customers to upload software test results has stolen the credentials and API tokens for thousands of organisation’s development environments.
Codecov is a tool used to track what percentage of an application’s source code has been exercised during software testing. To do this, it is integrated into the software build and test systems (Continuous Integration) of its customers who use a script to upload the output of test scripts into the Codecov system. It is this upload script that was compromised to also send copies of environment variables to a server controlled by the attacker. In order for CI systems to work, environment variables will typically contain user credentials, API tokens and other sensitive information needed to access and update source code and publish code changes to test or even production servers.
According to a security advisory from Codecov affected customers could have compromised:
- Any credentials, tokens, or keys that our customers were passing through their CI runner that would be accessible when the Bash Uploader script was executed.
- Any services, datastores, and application code that could be accessed with these credentials, tokens, or keys.
- The git remote information (URL of the origin repository) of repositories using the Bash Uploaders to upload coverage to Codecov in CI.
The unauthorised changes to the Codecov script have been traced back to January 31st 2021, and several changes were made to the script between then and when the changes were spotted on 1st April 2021. The changes were finally caught when a customer realised that the checksum (shasum) published by Codecov for the script file was different from the checksum calculated for the file the customer had just installed.
According to Codecov, an error in their Docker Image creation process left a credential exposed which the attackers were able to extract and then use to modify the uploader script customers install onto their systems.
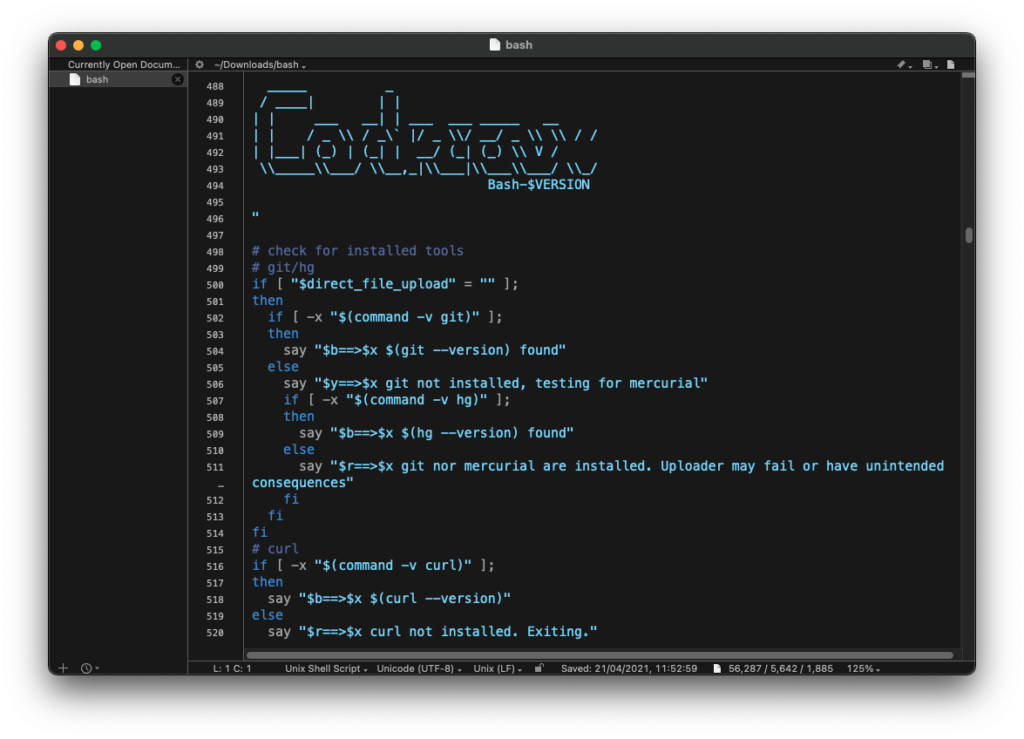
Codecov advises customers to check for this following string in the uploader script they have been using – if it exists then they have been using the compromised script and their credentials stored in environment variables have been exfiltrated:
curl -sm 0.5 -d “$(git remote -v)
How checksums help protect against supply chain attacks
A checksum or hash is a means of validating the integrity of a file – to prove it has not been changed during transmission or since it has been downloaded. Even a minor change to the file, will result in a different hash value being calculated.
Confirming the checksum for third party files installed into your network can help detect unauthorised changes or corruptions to those files from within the supply chain.
According to Reuters, many if not all of Codecov’s 19,000 customers including the likes of HP Enterprise, IBM and Atlassian could have their development environment credentials compromised through this attack raising the spectre of unauthorised code changes or intellectual property theft for those organisations.
Like the Solar Winds compromise earlier this year, the Codecov attack highlights the potential risk posed by even ‘trusted’ suppliers who provide code which is run in the heart of our networks and yet can be changed at any time.


















“We were very impressed with the service, I will say, the vulnerability found was one our previous organisation had not picked up, which does make you wonder if anything else was missed.”
Aim Ltd Chief Technology Officer (CTO)